Sicurezza e Privacy per la casa intelligente - CYBERSECURITY & RISK MANAGEMENT PROGRAM
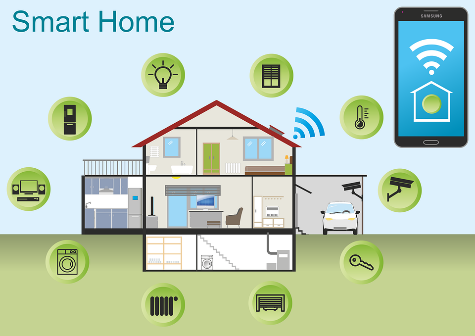
La domanda di soluzioni per la casa intelligente cresce. Il Webinar “Quanto è sicura la tua Smart Home?” del 16 Aprile affronterà il tema dei rischi cyber.

SOC As A Service Rockwell Automation

2013 Italian Report on Cyber Security - Critical Infrastructure and other sensitive sectors readiness

Sicurezza e Privacy per la casa intelligente - CYBERSECURITY & RISK MANAGEMENT PROGRAM

Insider Threat: significato ed esempi

Zero Trust Architecture and Solutions

CYBERSECURITY: La prima Guida in Italiano sulla Sicurezza Informatica: le Migliori Strategie per restare al Sicuro Online a casa evitando attacchi Hacker, Proteggere i dati sensibili ed evitare Truffe : Seidl, William

Information security training: oltre 4.888 foto stock acquisibili in licenza esenti da diritti d'autore

Computer Security @ POLIMI

Industrial Cybersecurity Services

Le linee guida ENISA per la cyber security della supply chain - Cyber Security 360

Operazioni integrate